Memory & Context Management
-
 1,219
1,219Data Center Firewall Toolkit
Discover how USI Insurance Services, a large insurance brokerage, transformed its nationwide network by implementing Fortinet Secure SD-WAN and Next-Generation…
Read More » -
 1,290
1,290Protect your business from viruses and data leaks
Running a small business is hard enough without worrying about hackers, data leaks, or malicious links. Let Kaspersky Small Office Security take…
Read More » -
 1,284
1,284The Gorilla Guide® To… Security and Governance for AI
Ein kleines Unternehmen zu führen ist schon schwer genug, ohne dass man sich über Hacker, Datenlecks oder bösartige Links…
Read More » -
 1,311
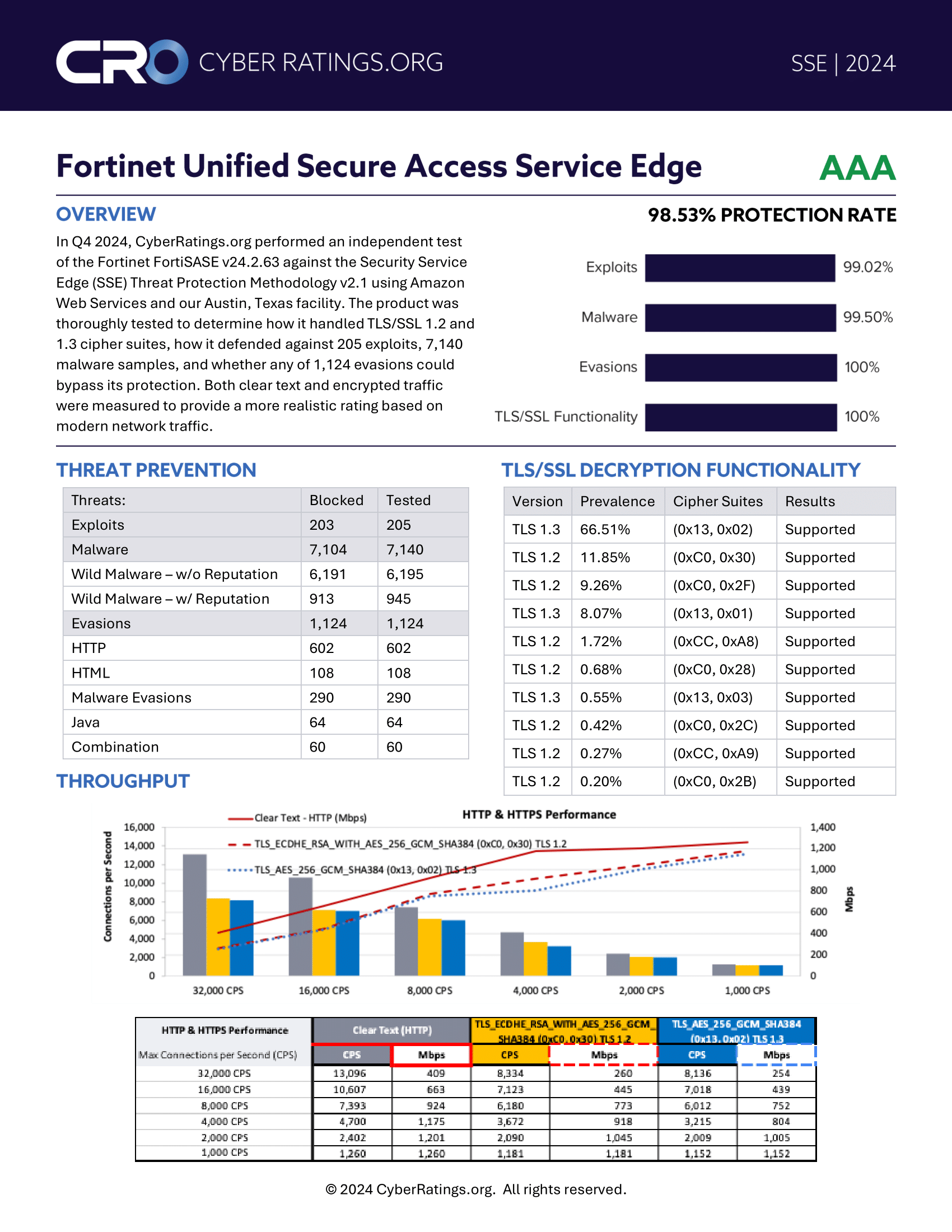
1,311FortiSASE Achieves ‘AAA’ Rating from CyberRatings.org
Independent validation of Fortinet’s Secure Access Service Edge Solution CyberRatings.org’s rigorous testing confirms FortiSASE’s exceptional performance in threat protection,…
Read More » -
 1,282
1,282Is SD-WAN Still Relevant in the Era of SASE, AI, and Zero Trust?
Explore the evolving role of SD-WAN amidst emerging technologies and security paradigms. Navigate the intersection of networking and security with…
Read More » -
 1,294
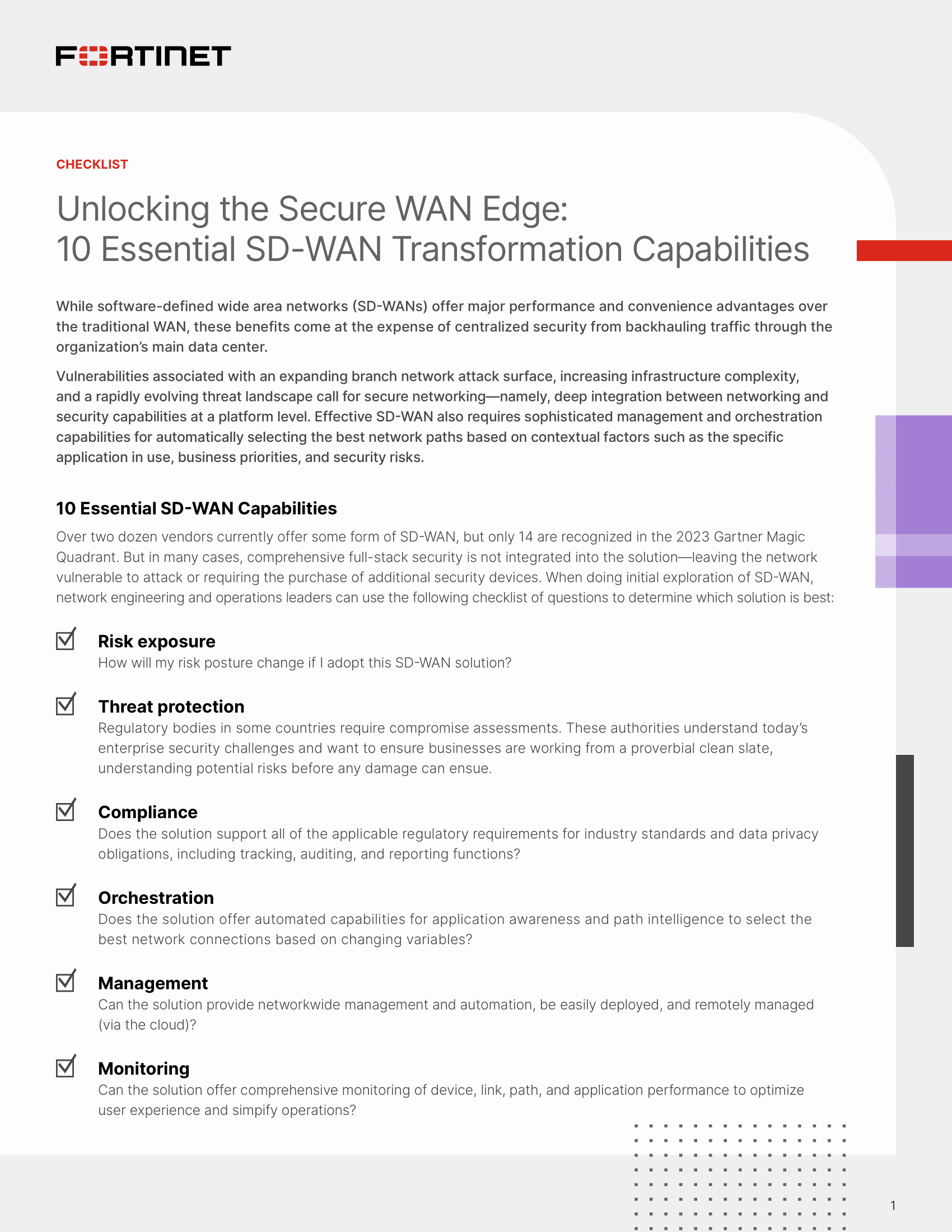
1,29410 Essential SD-WAN Transformation Capabilities
10 Essential SD-WAN Transformation Capabilities Use our comprehensive checklist to identify the SD-WAN solution that will best meets your…
Read More » -
1,310
Strike a Balance by Uncovering your Blind Spots
s your business held back by unseen challenges in consumer demand, operations, and costs? Discover how SAS® Intelligent Planning helps…
Read More » -
1,277
Harness the power of AI: A guide to modernizing your workplace
In the new era of technology, Dell AI PCs powered by Intel® Core™ Ultra offer a boost in productivity leveraging…
Read More » -
1,276
Cortex XSIAM: The Machine-Led, Human-Empowered Security Platform
The AI-Driven Security Operations Platform for the Modern SOC In the last few years, the needs of the security…
Read More » -
1,287
XSIAM Buyer’s Guide: How to Transform Your SOC for the AI Era
SOC teams need the right models, resources, and data to handle the volume and sophistication of threats seen on networks…
Read More »