cyber security
-
GEP Spend Category Outlook Report 2026: Indirect and Direct Spend
Procurement enters 2026 with sharper mandates and tighter constraints. Spend categories are shifting, not just in price but also in…
Read More » -

Guardians of the Workflow – How Financial Firms Govern Content Without Slowing Down Business
Content governance is a mission-critical function for financial services firms—without it, they cannot stay in business. Now far from a…
Read More » -

Sharper CIMs Start with Smarter Signals
Too many CIMs rely on recycled boilerplate and internal claims that don’t hold up under scrutiny. Buyers want defensible insights,…
Read More » -
Risikominderung für morgen durch Upgrade auf Dell Copilot+ PCs
Nicht alle KI‑PCs sind gleich. Dieses eGuide erläutert die Unterschiede zwischen Einstiegs‑KI‑PCs mit schwächeren NPUs und fortgeschrittenen Systemen mit über…
Read More » -
Dell Pro 14 Essential Dell Pro 15 Essential – Business-fähige Laptops mit unerlässlichen Sicherheits
Die Dell Pro Essential Serie, bestehend aus Dell Pro 14 Essential und Dell Pro 15 Essential, bietet geschäftstaugliche Laptops für…
Read More » -
Buyer’s Guide to Exposure Assessment and Management Platforms
Every day, security teams face the same problem: too many findings, too little context, and limited time to act. Long…
Read More » -
Kaufberater: Plattformen für Expositionsbewertung und -Management
CTEM ist mehr als ein weiterer Security-Baustein. Mit einem CTEM-Programm schaffen Sie das nötige operative Framework für umfassende Transparenz mit…
Read More » -
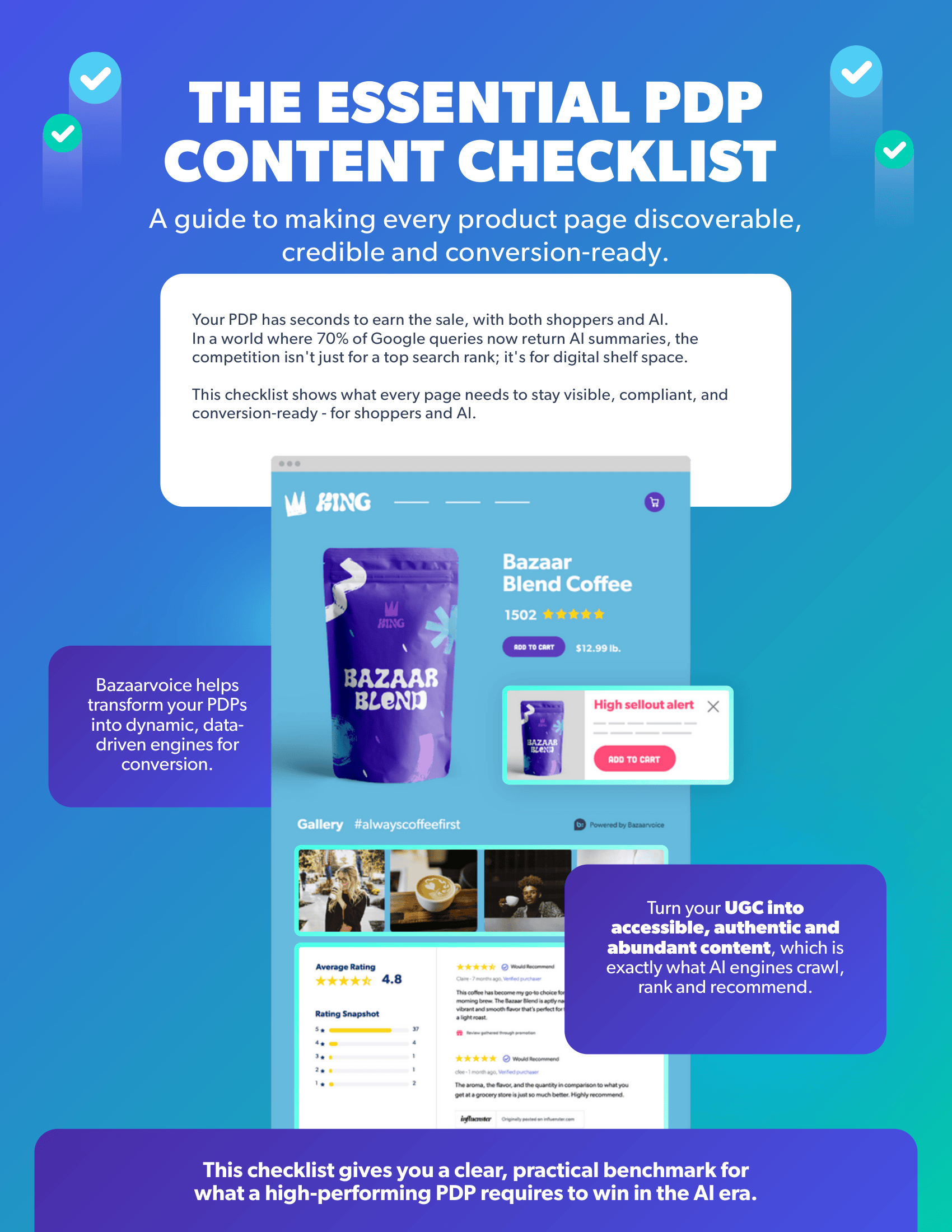
The essential PDP content checklist
Is your product detail page (PDP) content a hidden liability? In the new AI economy, you have seconds to prove…
Read More »
