Security Automation
-
Das Ende des traditionellen SIEM und der Aufstieg von Incident Command
Das Ende des traditionellen SIEM und der Aufstieg von Incident Command Das SIEM von vor 20 Jahren wird von modernen…
Read More »
With the rapid rise of agentic AI, non-human identities (NHIs) have quietly become the largest, least-governed attack surface in the…
Read More »Ob Sie den Kampf für Cybersicherheit gewinnen oder verlieren, hängt davon ab, ob Sie in der Lage sind, Informationen über…
Read More »
How AI is Emerging in GovTech: A Guide for Future-Ready Public Sector Finance Teams Artificial intelligence is no longer a…
Read More »C’est une réalité d’aujourd’hui : les entreprises doivent fournir à leurs col- laborateurs distants un accès sécurisé et authentifié aux…
Read More »Security leaders are recognizing that modern data security requires more than enforcement—it demands visibility into the data, the activities, and…
Read More »Das Ende des traditionellen SIEM und der Aufstieg von Incident Command Das SIEM von vor 20 Jahren wird von modernen…
Read More »
Effective procurement processes are the backbone of organizational success—much like a well-orchestrated river, where every drop moves in harmony toward…
Read More »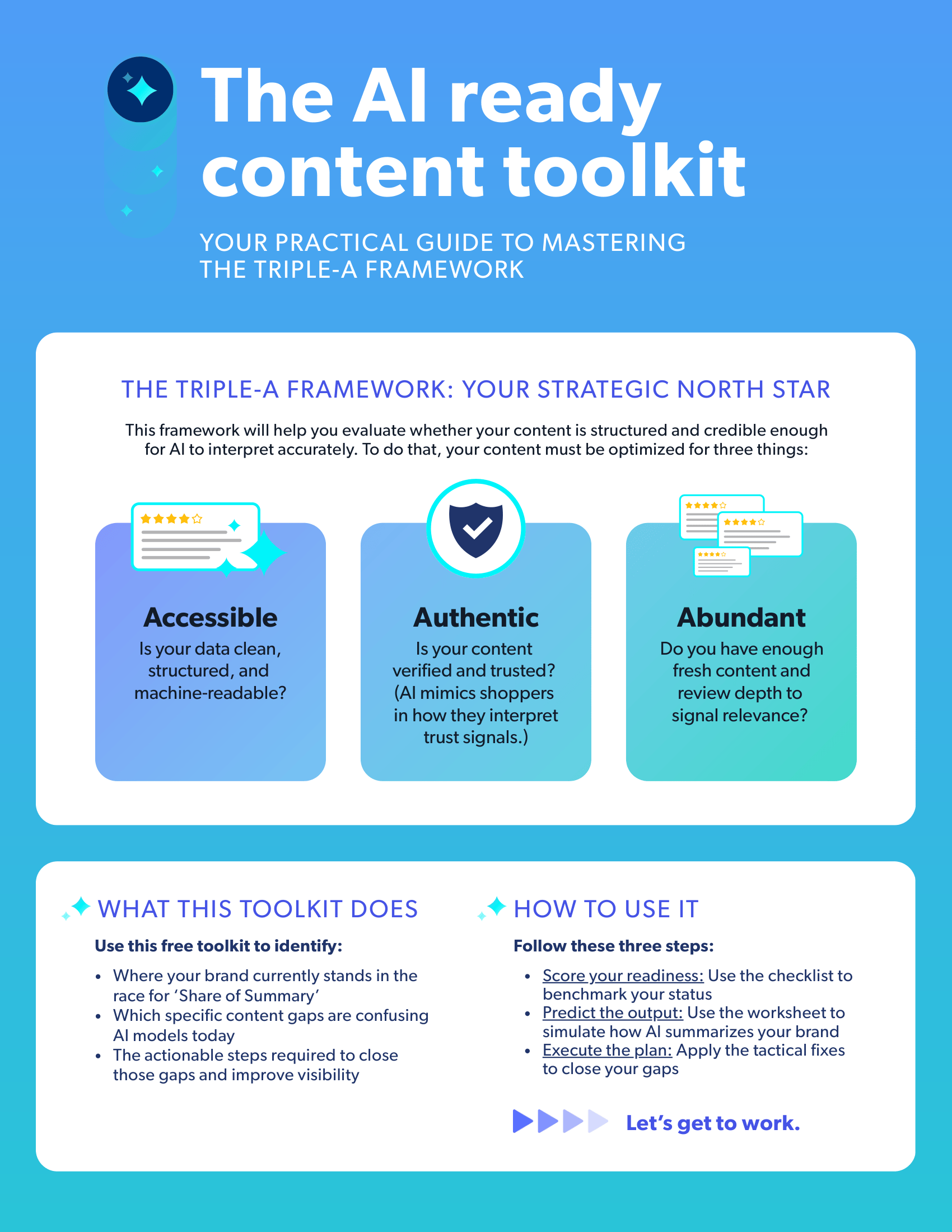
While AI uses many signals to make these decisions, user-generated content (UGC) remains one of the most powerful trust signals.…
Read More »
To compete at the edge of innovation, modern teams need fast, intelligent tools that help them maximize the value of…
Read More »
Document workflows are slow and complex, but Acrobat Studio makes them faster and smarter with new AI-powered tools. It helps…
Read More »