Security Operations
-
Empower the Hybrid Workforce with the Right SASE Approach
The New Perimeter is Everywhere—Your Security Should Be Too With more users working beyond traditional walls, securing remote access…
Read More »
This checklist outlines the essential capabilities network engineering and operations leaders should seek in an SD-Branch solution. It emphasizes the…
Read More »
For organizations struggling to manage distributed branch networks efficiently, this toolkit offers valuable insights and real-world examples of successful SD-Branch…
Read More »
This toolkit provides a guide to effective SD-Branch management, emphasizing the need for automation and orchestration to handle the increasing…
Read More »
This Forrester Total Economic Impact™ study examines the potential return on investment enterprises can realize by deploying Fortinet NGFW for…
Read More »
Discover how USI Insurance Services, a large insurance brokerage, transformed its nationwide network by implementing Fortinet Secure SD-WAN and Next-Generation…
Read More »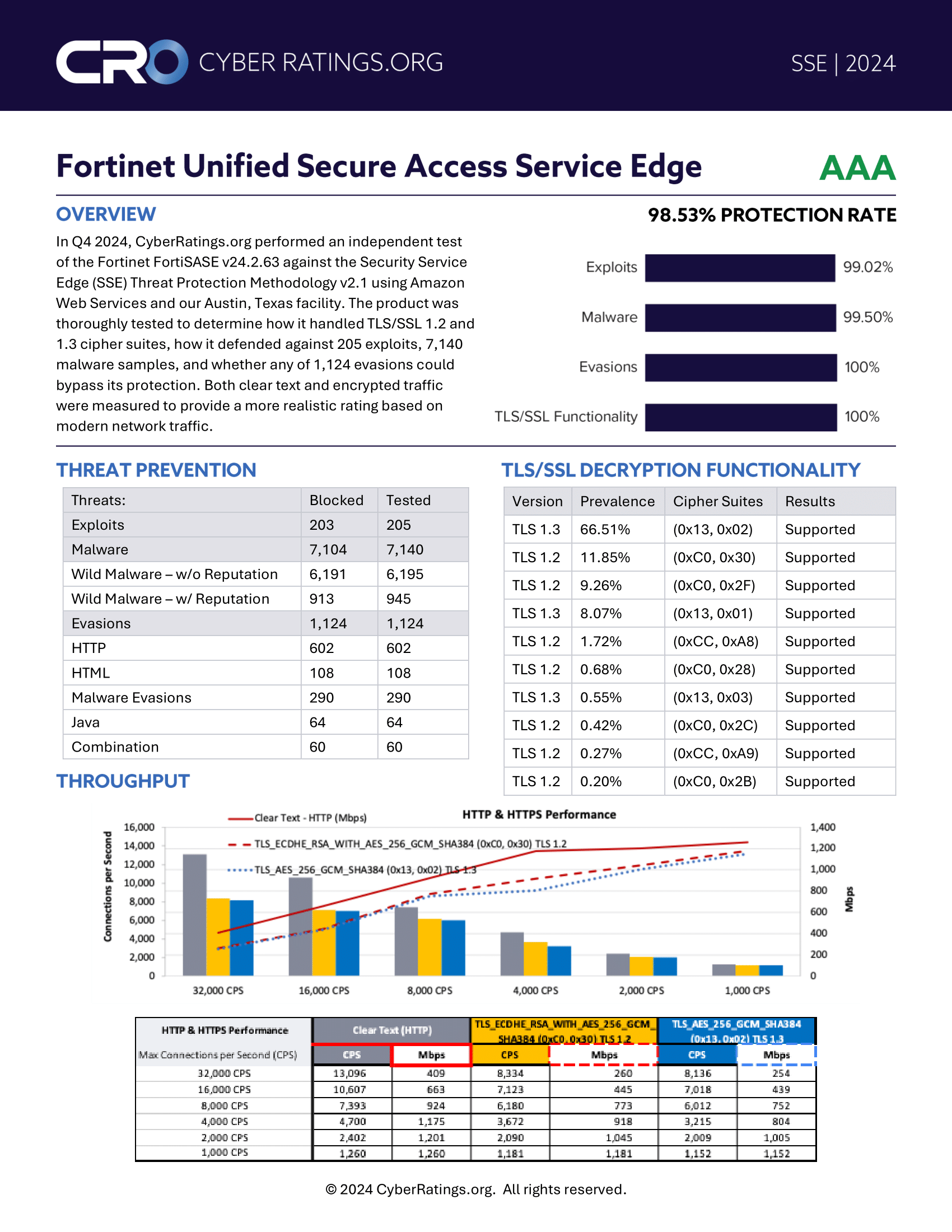
Independent validation of Fortinet’s Secure Access Service Edge Solution CyberRatings.org’s rigorous testing confirms FortiSASE’s exceptional performance in threat protection,…
Read More »
Help identify what’s missing—and how to fix it with Fortinet’s Unified SASE Checklist In the evolving landscape of hybrid work,…
Read More »Ready to Rethink Remote Access? Discover how Fortinet helps secure and streamline hybrid work environments Traditional perimeter-based architectures are struggling…
Read More »
The New Perimeter is Everywhere—Your Security Should Be Too With more users working beyond traditional walls, securing remote access…
Read More »
A Buyer’s Guide to Zero-Trust Network Access Having an excellent ZTNA Solution is important because since the pandemic the hybrid…
Read More »