Development
-
Navigating the triple threat of a volatile regulatory landscape
At first glance, companies seem to have regulatory compliance under control. Few notice any obvious gaps. But beneath this superficial…
Read More » -

AI in Action: How Rapid7 is Redefining Security Operations
AI is transforming cybersecurity, and Rapid7 is at the forefront of integrating AI across our platform. In this session, we’ll…
Read More » -
Anatomy of an Attack Infographic
Walk through the anatomy of a real-world cyberattack with Rapid7 experts. In this infographic, learn how attackers think, move, and…
Read More » -
The End of Legacy SIEM and the Rise of Incident Command
The SIEM of 20 years ago is being outpaced by modern attackers. In this paper, Rapid7 shares the way legacy…
Read More » -
First 24 Hours of a Cyberattack eBook
What really happens in the first 24 hours of a cyberattack? In this eBook, we walk through a real-world zero-day…
Read More » -

Using Security to Speed up Development
Forget what you know about security being a blocker on speed. Find out how elite engineering teams are actually using…
Read More » -
The AI Adoption Paradox
In 2025, use of AI in software development is marked by two paradoxes: the paradox of mistrust, and the paradox of…
Read More » -
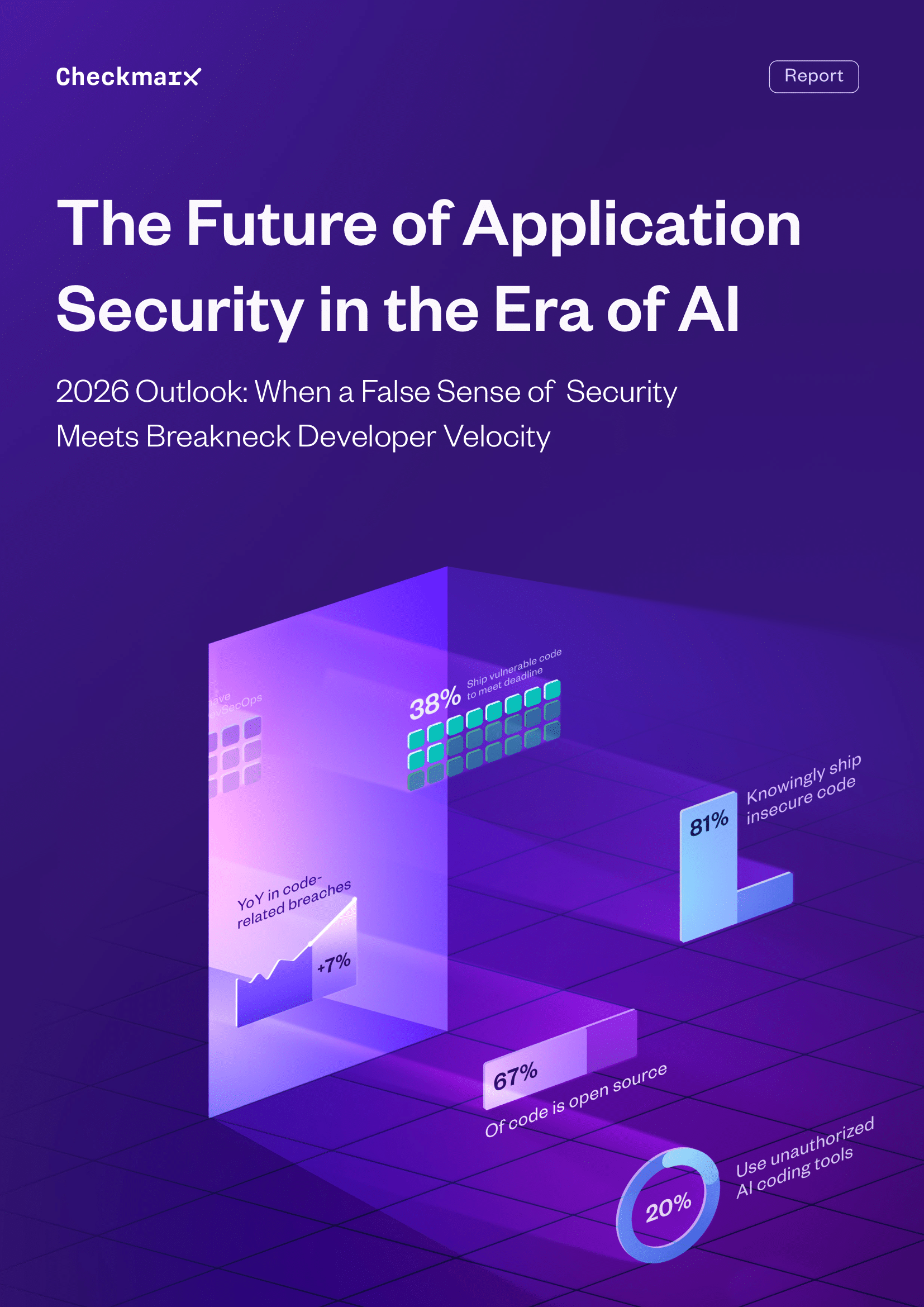
The Future of AppSec in the Era of AI
What happens when speed overtakes security and no one hits the brakes? Organizations are racing to deploy faster than ever,…
Read More » -
Securing Agentic AI-driven Development
Navigate the Next Frontier of Application Security The rapid adoption of agentic, AI-driven code generation is redefining the way organizations…
Read More » -

Catch Attackers Before They Strike: Early Warning Insights for Software Supply Chain Attacks
Open-source software libraries form the backbone of modern application development. Their inherent transparency and community-driven development foster a rapid pace…
Read More »